Earlier this year, McAfee researchers predicted in the McAfee Mobile Threat Report that we expect the number of targeted attacks on mobile devices to increase due to their ubiquitous growth combined with the sophisticated tactics used by malware authors. Last year we posted the first public blog about the Lazarus group operating in the mobile landscape. Our recent discovery of the campaign we have named RedDawn on Google Play just a few weeks after the release of our report proves that targeted attacks on mobile devices are here to stay.
RedDawn is the second campaign we have seen this year from the “SunTeam” hacking group. In January, the McAfee Mobile Research Team wrote about Android malware targeting North Korean defectors and journalists. McAfee researchers recently found new malware developed by the same actors that was uploaded on Google Play as “unreleased” versions. We notified both Google, which has removed the malware from Google Play, and the Korea Internet & Security Agency.
Our findings indicate that the Sun Team is still actively trying to implant spyware on Korean victims’ devices. (The number of North Korean defectors who came to South Korea exceeded 30,000 in 2016, according to Radio Free Asia.)Once the malware is installed, it copies sensitive information including personal photos, contacts, and SMS messages and sends them to the threat actors. We have seen no public reports of infections. We identified these malwares at an early stage; the number of infections is quite low compared with previous campaigns, about 100 infections from Google Play.
Malware on Google Play
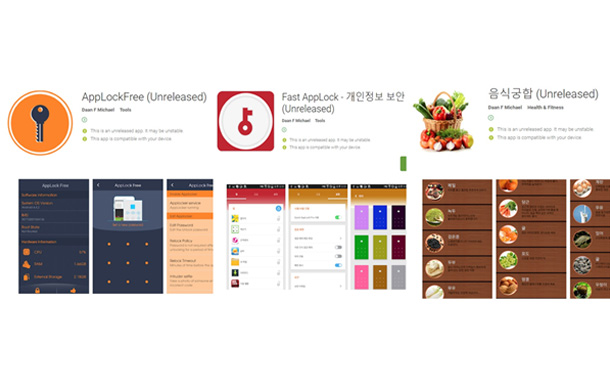
Malware uploaded on Google Play (now deleted).
We found three apps uploaded by the actor we named Sun Team, based on email accounts and Android devices used in the previous attack. The first app in this attack, 음식궁합 (Food Ingredients Info), offers information about food; the other two apps, Fast AppLock and AppLockFree, are security related. 음식궁합 and Fast AppLock secretly steal device information and receive commands and additional executable (.dex) files from a cloud control server. We believe that these apps are multi-staged, with several components. AppLockFree is part of the reconnaissance stage we believe, setting the foundation for the next stage unlike the other two apps. The malwares were spread to friends, asking them to install the apps and offer feedback via a Facebook account with a fake profile that heavily promoted 음식궁합.
Links to previous operations
After infecting a device, the malware uses Dropbox and Yandex to upload data and issue commands, including additional plug-in dex files; this is a similar tactic to earlier Sun Team attacks. From these cloud storage sites, we found information logs from the same test Android devices that Sun Team used for the malware campaign we reported in January. The logs had a similar format and used the same abbreviations for fields as in other Sun Team logs. Further, the email addresses of the new malware’s developer are identical to the earlier email addresses associated with the Sun Team. The relationship among email addresses and test devices is explained in the following diagram.
The use of identical email addresses ties the two malware campaigns to the same attacker.
By Jaewon Min, McAfee